
How to design thoughtful and secure cross domain workflows
Senior technologists, architects, and service designers across government, are at the forefront of creating brilliant public services. They’re implementing robust solutions that protect sensitive information, and ensure efficient and cost effective public sector operations.
A critical component in digital transformation moving forward is the implementation of Cross Domain Workflows (CDWs). These workflows enable secure data exchange between different security domains, such as between a high-side (SECRET) and low-side (OFFICIAL) environment.
In this blog, we’ll explore some of the more technical aspects of cross domain workflows, focusing on key concepts, outlining some of the cryptographic techniques, and discussing how they can be effectively implemented using modern tools.
Understanding cross domain workflows
A CDW allows for the secure transmission and interaction of data across different security levels. For government agencies, this means gathering data from public-facing, less secure systems (low side) and processing it in highly secure environments (high side). This dual-environment approach helps protect sensitive data from sophisticated cyber threats while maintaining accessibility and usability for necessary operations.
Key concepts and components
To establish a secure CDW, several key components and cryptographic techniques are involved:
- Elliptic Curve Diffie-Hellman (ECDH) Key Exchange:
- ECDH is a public-key cryptography protocol that allows two parties to establish a shared secret over an insecure channel. This shared secret can then encrypt communications, ensuring that data remains confidential even if intercepted.
- AES-GCM Encryption:
- Advanced Encryption Standard (AES) in Galois/Counter Mode (GCM) is a symmetric encryption algorithm known for its performance and security. AES-GCM provides both confidentiality and integrity of data, making it suitable for secure data transmission.
- Web Crypto API:
- This is a standard API for performing cryptographic operations in web applications. It supports a variety of cryptographic algorithms, including ECDH and AES-GCM, enabling secure communications directly from client-side applications.
- Python Cryptography Library:
- This library provides cryptographic recipes and primitives to Python developers. It includes support for ECDH, AES-GCM, and other cryptographic functions necessary for implementing secure CDWs.
Implementing key exchange and encryption
Client-side encryption pattern
On the client side, the Web Crypto API handles key generation, key exchange, and data encryption.
- Key Generation:
- The client generates an ECDH key pair.
- Key Exchange:
- The client’s public key is shared with the server, and the server’s public key is imported.
- Shared Secret Derivation:
- Using the client’s private key and the server’s public key, a shared secret is derived.
- Data Encryption:
- The shared secret is used to derive a symmetric AES-GCM key, which is then used to encrypt the data.
- Transmission:
- The client sends the encrypted data, initialisation vector (IV), and its public key to the server.
Server-side key management and encryption pattern
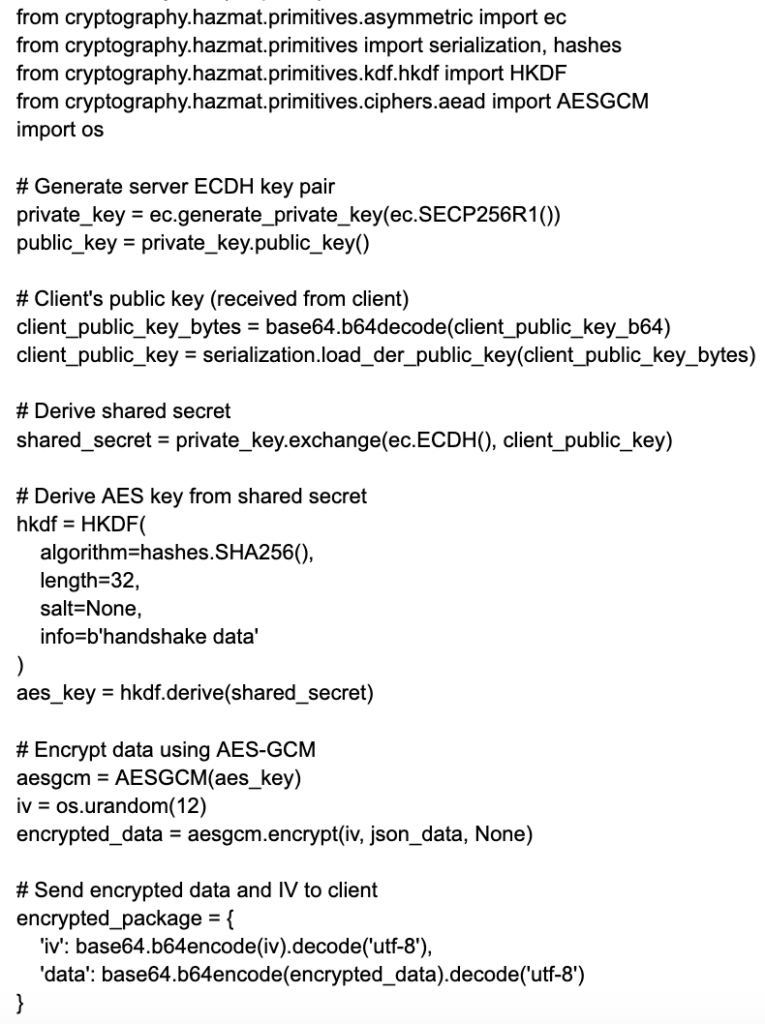
On the server side, the Python Cryptography library handles key generation, key exchange, and data encryption/decryption.
- Key Generation:
- Generating ECDH key pairs for both the high side and low side.
- Key Storage:
- Storing the keys securely, typically in a key vault.
- Encryption:
- Using the server’s private key and the client’s public key to derive the shared secret, followed by data encryption using AES-GCM.
Example: Encryption workflow
Let’s illustrate the encryption workflow with a simplified, high-level example.
Key generation
- Server generates ECDH key pairs for both the high and low sides.
- Private keys are serialised and stored securely.
- Public keys are also serialised and stored for easy access.
Data encryption
- Client generates an ECDH key pair and sends its public key to the server.
- Server imports the client’s public key and uses its high side private key to derive a shared secret.
- The shared secret is used to derive an AES-GCM key.
- Data is encrypted with this AES-GCM key, and the IV and encrypted data are returned to the client.
# Server-side Python (simplified)
Security considerations
While implementing CDWs, it’s essential to address several security considerations.
- Key Management:
- Properly manage and protect cryptographic keys to prevent unauthorised access.
- Data Integrity:
- Use authenticated encryption (like AES-GCM) to ensure that data has not been tampered with.
- Access Controls:
- Implement strict access controls to limit who can access and manipulate keys and encrypted data.
- Regular Audits:
- Conduct regular security audits to identify and mitigate potential vulnerabilities.
By leveraging ECDH for key exchange and AES-GCM for encryption, cross domain workflows provide a robust framework for securing sensitive government data. As senior technologists and architects, your role in designing these workflows is crucial to maintaining data integrity and confidentiality. By implementing these cryptographic techniques thoughtfully and rigorously, you can help safeguard critical information and ensure that your systems are resilient against sophisticated cyber threats.
Secure service design with CDWs
One of the most critical principles is to ensure that users on their own machines have as few demands placed on them as possible.
Most users lack the expertise to deal with encryption keys or understand complex security protocols. By abstracting technical complexities and minimising the cognitive load on users, we create more secure and user-friendly experiences. This approach not only enhances security but also improves overall user satisfaction.
Minimising user demands is the key to better security
Users should not be burdened with complex security operations. Instead, they should experience a seamless interaction where the underlying security measures are transparent. For instance, rather than presenting a user with a single, large vetting form, we can break down the process into smaller, manageable tasks spread over several days. This method, often called gamification, can improve user engagement and reduce the likelihood of errors or fatigue.
Key Benefits of burden reduction
- Reduced Cognitive Load:
- Smaller, more manageable tasks are less intimidating and easier for users to complete accurately.
- Improved Engagement:
- Spreading tasks over time makes the process feel less overwhelming and more engaging.
- Enhanced Security:
- Smaller, incremental data submissions are easier to monitor and verify for security purposes.
The concept of information slices
In secure service design, an information slice refers to a discrete, manageable piece of a larger data set. By handling data in slices, we can optimise operational efficiency and security. This approach is particularly useful in environments with varying levels of data sensitivity and access permissions.
Why do information slices matter?
- Operational Practicality:
- Handling data in smaller slices allows for more efficient and manageable workflows, particularly in environments with mixed sensitivity levels.
- Enhanced Security:
- Sensitive aggregate data sets can be kept in high-security environments (high side), while less sensitive slices can be processed in lower security environments (low side). This approach reduces the risk of exposure and ensures that the most sensitive data is afforded the highest level of protection.
- Streamlined Processes:
- By processing slices of information at the low side, tasks can be distributed more effectively among staff who do not have high-side clearance. This distribution allows for a more dynamic and responsive operational framework.
READ: What is a cross domain workflow and why does it matter?
Practical application of cross domain workflows
CDWs are a great example of how slicing information can enhance both security and operational efficiency. In a typical scenario, aggregate data sets are (or should probably be!) maintained on the high side, where security controls are stringent. However, most staff operate on the low side and cannot access high-side environments directly.
Considerate CDW service design ensures we’re not creating more problems than we solve — for example, introducing or maintaining twin IT estates, or increasing the costs of sustaining a service by spreading it across two domains.
Example use case: vetting records
- High Side:
- Stores the complete aggregate vetting records, ensuring data integrity and security.
- Low Side:
- Handles individual slices of the vetting records, allowing staff to perform specific checks or administrative tasks without exposing the entire data set.
By implementing cross domain workflows, we maintain a high level of security for sensitive information while enabling practical and efficient processing on the low side. This approach ensures staff can perform their duties without unnecessary barriers, all while protecting the integrity and confidentiality of the overall data set.
In designing secure services, it’s crucial to balance the need for robust security measures with the goal of providing a user-friendly experience. By minimising the demands placed on users and leveraging the concept of information slices, we create secure, efficient, and user-centric services. Cross domain workflows exemplify how this balance can be achieved, ensuring that data remains protected while enabling practical and effective operations.
At Zaizi, our mission is to make the UK the best and safest place to live and work. We do this by helping our public sector customers solve complex problems.
If you want to discuss cross domain workflows, we can organise a transformation day and help you start the journey to more secure, sustainable, user-centric services.
Digital government is hard, together we’ll succeed.
If you’d like to to talk to James, discuss cross domain workflows or any of the points covered in this blog, please get in touch.
-

CyberUK 2026: the reality check government teams can’t ignore
-

Government and AI: Scaling adoption safely across the public sector
-

AI in government: Moving from hype to implementation reality
-

How learning from end users delivers data-driven improvements with real impact
-

Zaizi’s ScanApp collaboration with Border Force features in IBMATA magazine
-

AI in government: Key takeaways from our lunch and learn event
